The Best Guide To Risk Management Enterprise
Table of ContentsRisk Management Enterprise - QuestionsExcitement About Risk Management EnterpriseLittle Known Questions About Risk Management Enterprise.All About Risk Management EnterpriseNot known Factual Statements About Risk Management Enterprise The Best Guide To Risk Management EnterpriseThe Main Principles Of Risk Management Enterprise
Below are a few of its vital attributes that centers should understand. Take an appearance. Real-Time Danger Evaluations and Reduction in this software enable companies to constantly keep track of and evaluate threats as they evolve. This feature leverages real-time data and automated analysis to identify potential risks immediately. As soon as dangers are determined, the software facilitates immediate mitigation actions.
KRIs solve the problem of inconsistent or uncertain danger evaluation. They address the challenge of recurring threat administration by offering devices to keep an eye on threats constantly. KRIs boost protection threat oversight, guaranteeing that potential risks are identified and managed effectively. The task of threat administration must not be an obstacle. Consequently, companies must count on a first-class and advanced danger administration software program.
The Of Risk Management Enterprise
IT risk administration is a subset of venture threat monitoring (ERM), designed to bring IT risk according to a company's threat cravings. IT risk monitoring (ITRM) encompasses the policies, treatments and innovation required to decrease dangers and vulnerabilities, while preserving conformity with appropriate regulative demands. In enhancement, ITRM seeks to restrict the repercussions of harmful occasions, such as protection violations.
Veronica Rose, ISACA board director and an info systems auditor at Metropol Corp. The ISACA Threat IT framework straightens well with the COBIT 2019 structure, Rose said.
Enterprise Threat Monitoring Software Application Growth: Perks & Features, Expense. With technical developments, dangers are constantly rising. That being claimed, companies are most likely to encounter difficulties that impact their financial resources, procedures, and online reputation. From quickly rising and fall markets to regulatory adjustments and cyber risks, services browse via a constantly changing sea of risks.
The Greatest Guide To Risk Management Enterprise
In this blog site, we will study the world of ERM software application, exploring what it is, its benefits, attributes, and so on so that you can build one for your service. Venture Threat Monitoring (ERM) software program is the application program for planning, directing, arranging, and managing business activities and simplifying threat management processes.
With ERM, companies can make informative choices to improve the general strength of the organization. Read: ERP Application Growth Devoted ERM systems are critical for services that on a regular basis take care of huge amounts of sensitive details and numerous stakeholders to approve critical decisions. Some industries where ERM has actually come to be a standard system are medical care, financing, building and construction, insurance coverage, and infotech (IT).
: It is difficult for any kind of business to go through an extensive audit. It can be stayed clear of by using the ERM software system. This system automates policy compliance administration to maintain the company protected and compliant. Various other than that, it also logs and categorizes all the documents in the system making it easier for auditors to assess processes a lot faster.
Risk Management Enterprise - An Overview
You can additionally link existing software systems to the ERM using APIs or by including information manually. Businesses can use ERM to assess dangers based on their possible influence for far better threat monitoring and mitigation.: Including this feature enables users to get real-time notices on their devices concerning any risk that might take place and its impact.

Rather, the software application allows them to establish limits for various processes and send out press notices in instance of possible threats.: By integrating information visualization and reporting in the about his custom-made ERM software application, companies can acquire clear insights regarding threat patterns and performance.: It is compulsory for companies to follow sector conformity and regulatory requirements.
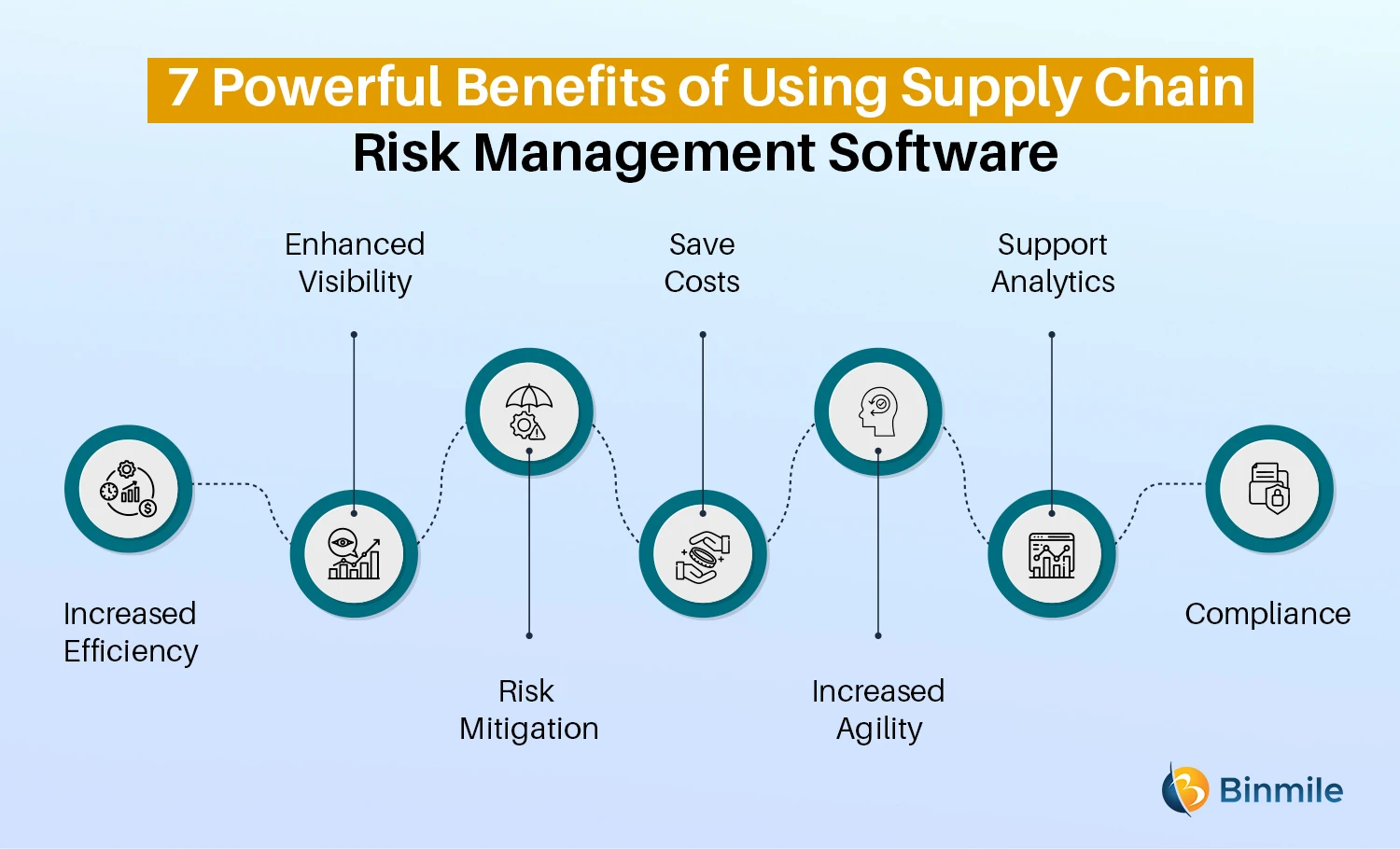
These systems enable companies to execute best-practice threat monitoring procedures that straighten with industry criteria, using an effective, technology-driven technique to determining, assessing, and mitigating threats. This blog site checks out the advantages of computerized danger management devices, the locations of threat management they can automate, and the value they bring to a company.
Risk Management Enterprise Fundamentals Explained
Teams can establish up forms with the appropriate fields and quickly produce various types for various danger kinds. These danger evaluation forms can be circulated for conclusion using automated process that send out notices to the pertinent team to complete the types online. If forms are not finished by the deadline, after that chaser emails are automatically sent out by the system.
The control tracking and control testing process can additionally be automated. Firms can utilize automated operations to send out regular control examination notifications and personnel can get in the outcomes via online kinds. Controls can also be monitored by the software application by setting regulations to send alerts based upon control information kept in other systems and spreadsheets that is drawn into the system using API assimilations.
Threat administration automation software can additionally support with risk coverage for all degrees of the business. Leaders can view records on risk exposure and control efficiency with a variety of reporting results consisting of static reports, Power BI interactive records, bowtie evaluation, and Monte Carlo simulations. The capability to draw actual time reports at the touch of a switch removes arduous information manipulation jobs leaving danger teams with even more time to evaluate the information and advise the company on the most effective course of action.
The need for effective has never been much more important. Risk Management Enterprise. Organizations operating in affordable, fast-changing markets can not manage delays or ineffectiveness in attending to prospective dangers. Standard risk management making use of hand-operated spreadsheet-based processes, while familiar, commonly lead to fragmented information, lengthy coverage, and an enhanced probability of human error. Automating the threat management process with software application addresses these shortcomings.
About Risk Management Enterprise
This ensures threat signs up are always present and lined up with organizational purposes. Compliance is another essential chauffeur for automating risk administration. Standards like ISO 31000, CPS 230 and COSO all supply advice around risk administration ideal techniques and control frameworks, and automated danger administration devices are structured to line up with these requirements helping companies to fulfill most commonly utilized danger monitoring standards.
Search for threat software platforms with a consents power structure to conveniently establish process for danger acceleration. This capability enables you to customize the view for every user, so they just see the information appropriate to them. Make certain the ERM software application provides user monitoring so you can see that entered what information and when.
Seek out tools that visit site use project threat monitoring abilities to handle your jobs and portfolios and the associated dangers. The benefits of adopting risk management automation software application expand far past effectiveness.
The Basic Principles Of Risk Management Enterprise
While the case for look at these guys automation is compelling, applying a risk administration system is not without its obstacles. To conquer the obstacles of threat administration automation, companies should spend in information cleansing and administration to guarantee a strong structure for executing an automated system.
Automation in threat monitoring empowers services to change their approach to risk and develop a stronger structure for the future (Risk Management Enterprise). The concern is no longer whether to automate danger monitoring, it's how soon you can begin. To see the Riskonnect at work,
The response typically lies in how well risks are prepared for and handled. Task administration software serves as the navigator in the troubled waters of project execution, offering tools that identify and examine threats and design methods to alleviate them successfully.